Over Labor Day weekend, nude photos of celebrities including Jennifer Lawrence and Kate Upton, were brought to the attention of Internet gossip fiend Perez Hilton, who then posted the images on his website. Along with Hilton’s blog, these pictures were also shared on anonymous online forums like 4chan and Reddit, according to The New York Times.
Soon after, however, Hilton removed the photos from his website and posted an apology video that expressed his sincere guilt and deep remorse for violating the privacy of these celebrities. But while the video might have appeased Hilton’s own feelings of regret and responsibility for spreading the images, it did nothing against the permanent power of the Internet, where once something is posted, it is nearly impossible to purge its existence.
While it is easy to point the finger at the perpetrators who hacked into these celebrities’ iCloud accounts and obtained the pictures, the real issue that comes into light is our generation’s overestimation of Internet security. Just because something takes place behind a computer screen, or in this situation a cell phone, does not ensure its guaranteed privacy. Just because something is “deleted” does not mean it is gone forever.
As computer-users, we are under the impression that when something is gone from our screens, then it has been thrown out into virtual trash and taken out to the virtual garbage dump, where it disappears.
This is not the case, and the leaking of nude celebrity photos highlights this misconception of Internet security.
Google, for example, stores everything you store. E-mails, web searches, pictures, contacts, calendar events. Anything you’ve ever clicked, liked, searched, posted, commented or typed is accessible, according to CNN.
But Google itself is not the problem (what can they really do with my most recent web search of the nearest Chipotle?). It becomes a problem when hackers access this information. And still, one might ask, what can a hacker do with my most recent web search of the nearest Chipotle? Based on that search, they can find out where I am in no time at the simple click of a button.
Hacking into a computer might even be easier than breaking into a house, and yet we are not cautious in what we post and where we post it. It is easy to underestimate the power of a hacker because a sense of ownership and privacy is assumed every time we open our devices; this is my phone, this is my computer, so my actions are confined only to these screens.
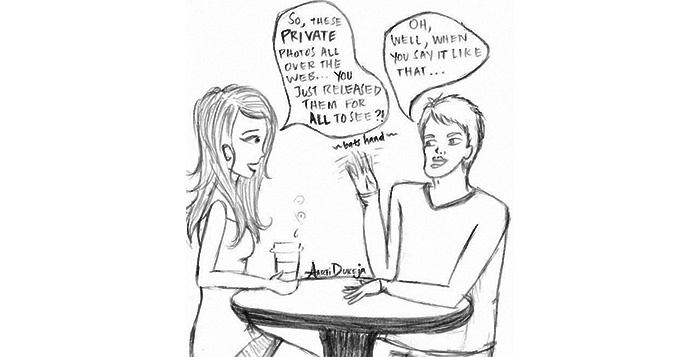
But these actions we expect to exist under our eyes and our screens only can easily be shared with millions of other eyes and millions of other screens. We want to believe that our security is invincible, that our accounts are impenetrable. But the system is not foolproof. There are loopholes and ways to breach the screens, and hackers dedicate their lives to exploiting these faults.
Since we grew up during the social media boom where everything is shared with everyone, it is only natural for us to disregard the security of all our technology. We use usernames, we install antivirus software, we create passwords and expect our devices to be protected.
Yet, there are still instances time and time again, as most recently presented in the nude celebrity photographs that were leaked, that highlight the weaknesses of a network into which we place so much trust.
Among these web blunders, it is easy to forget the purpose of the Internet and what it has done for the world. This global connection of networks allows us to access endless amounts of information, communicate with people around the world and further advance technological progress, to name a few. But this powerful tool can also cause harm.
While some may blame Jennifer Lawrence and Kate Upton for being foolish and careless of their cyberspacial possessions, they alone are not guilty. Instead, maybe our generational mindset is to blame for the fact that we live in such a technology-dependent world. We must always be mindful of such actions carried out on the web and be cognizant of their potential consequences.
-By Zoe Elfenbein
The Emory Wheel was founded in 1919 and is currently the only independent, student-run newspaper of Emory University. The Wheel publishes weekly on Wednesdays during the academic year, except during University holidays and scheduled publication intermissions.
The Wheel is financially and editorially independent from the University. All of its content is generated by the Wheel’s more than 100 student staff members and contributing writers, and its printing costs are covered by profits from self-generated advertising sales.